Data privacy is a looming concern for consumers and thus securing sensitive data should be paramount for direct mail marketers. Data breaches can have severe repercussions, such as financial loss, identity theft, reputational damage, and legal consequences. All of which can be prevented by implementing strict security measures.
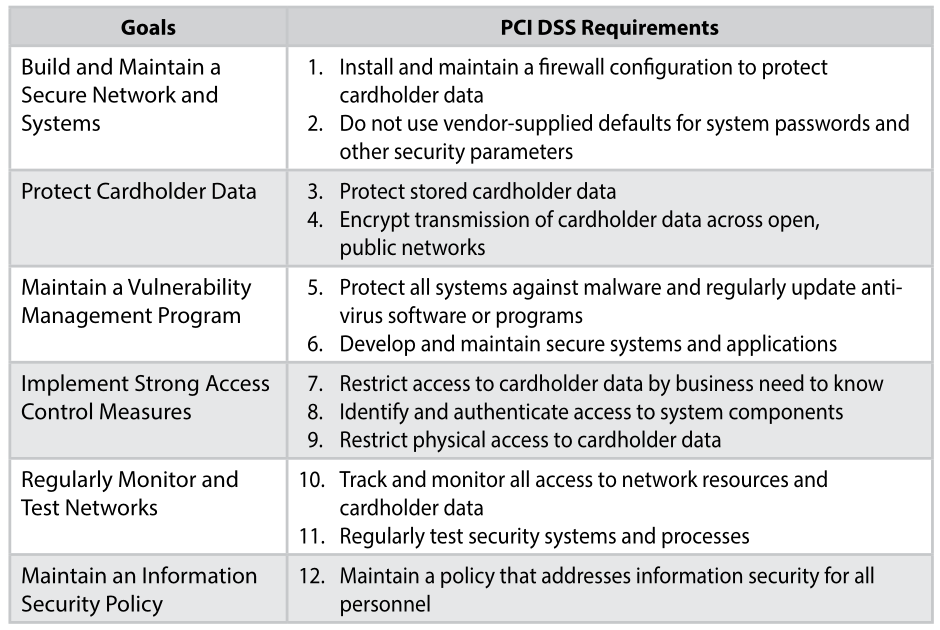
As a leader in direct mail marketing, we adhere to industry best practices and prioritize robust data security measures that enable us to offer personalized direct mail campaigns while respecting privacy and maintaining trust. Nahan maintains compliance certifications like PCI DSS Level 2, AICPA SSAE18 SOC2 Type 2 + HITRUST CSF, HIPAA, and GDPR compliance. We also engage third-party auditors to conduct security audits, penetration tests, and risk assessments, validating our security measures and identifying areas for improvement.
It’s important that marketers understand the risks, impacts, and regulatory requirements associated with direct mail campaigns, and how Nahan employs key security measures in response. Let’s dive in!
Importance of Protecting Sensitive Customer Data in Direct Mail Campaigns
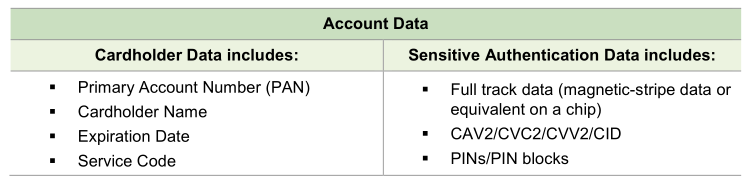
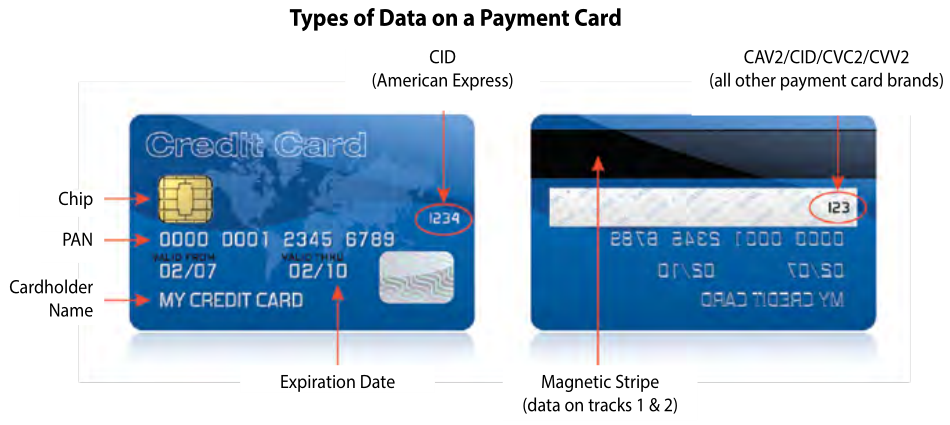
In today’s digital age, where data breaches and privacy concerns are prevalent, protecting sensitive customer data is of utmost importance in direct mail campaigns. Direct mail involves the collection, storage, and processing of customer information, such as names, addresses, credit card details, purchase history, and other financial information. Safeguarding this sensitive customer data should be a top priority for businesses engaging in direct mail marketing. It is essential that direct mail providers implement robust security measures to ensure the confidentiality, integrity, and availability of this data.
“We live in a world where consumers want both personalization and data security. In response, direct mail marketers must work with a trusted partner who has industry knowledge, integrity, and rock-solid security measures. At Nahan, I’m proud to say we have all three.”
-Elizabeth Evans, Security Administrator
Common Security Threats and Solutions
When it comes to direct mail campaigns, several common threats pose risks to the security of sensitive customer data. Understanding these threats is essential for implementing effective security measures.
Threat: Data Interception and Breaches
During the transmission of customer data, interception by malicious actors can occur, compromising the confidentiality of the information. Intercepted data can be exploited for identity theft, fraud, or other malicious activities.
Nahan’s Response: Data Encryption and Protection
Data encryption transforms sensitive information into unreadable code, securing it against unauthorized access. It applies to data transmission, data storage, and physical documents, with key practices including using strong encryption algorithms, secure key management, end-to-end encryption, regular updates of encryption protocols, and regular security audits and training.
Nahan’s robust information security program adheres to international standards, ensuring comprehensive data governance and privacy protection. We continually monitor our systems and data to detect suspicious activities or potential security breaches. In the event of any security incidents, our incident response team follows a predefined process that includes containment, investigation, mitigation, and recovery.
Nahan emphasizes continuous improvement and ongoing training. Regular security training sessions raise employee awareness about data protection best practices and emerging threats. We also conduct regular risk assessments and vulnerability scanning to identify and address any security weaknesses promptly. By analyzing and learning from security incidents, we continually enhance our data protection measures and mitigate future risks.
Threat: Unauthorized Access
Unauthorized individuals gaining access to customer data can lead to misuse or theft of sensitive information. This can occur through physical breaches, such as theft of mail or documents, or through cyberattacks targeting digital systems and databases.
Nahan’s Response: Access Control and Authentication
Access control limits unauthorized access to sensitive data, with strong passwords, role-based access controls, and regularly updated user access privileges. Multi-factor authentication adds an extra layer of security, requiring multiple factors of authentication. We also promote a security-conscious workforce through regular employee training.
Nahan implements physical security measures, including access control systems, video surveillance, and equipment protection measures like fire suppression systems and uninterruptible power supply (UPS), to protect premises and sensitive equipment.
Threat: Disaster
There is always the risk of the unthinkable happening, such as cyber-attacks, natural disasters, power outages, and equipment failure, among other disasters. Organizations of all sizes generate a large amount of data, with much of it extremely important to daily operations.
Nahan’s Response: Disaster Recovery and Business Continuity Planning
We have established a comprehensive Disaster Recovery Plan outlining procedures and protocols for responding to disruptions. Regular testing and refinement ensure its effectiveness, preparing Nahan to handle any unforeseen disruptions effectively.
Work With a Prepared Partner
What we’ve learned through seeing various organizations fail in the areas described above is that it is crucial to work with a partner you can trust. Your direct mail partner should be able to answer all of your security questions and have stringent measures to protect your customer data.
By prioritizing data governance, ongoing monitoring, incident response, continuous improvement, and employee training, Nahan ensures the highest level of protection for sensitive customer data in direct mail campaigns. Our commitment to data security enables our clients to have confidence in the integrity and confidentiality of their information throughout the direct mail process.